Virtual Private Networks (VPNs) are widely used for remote access to internal applications and data by businesses. However, despite their popularity, this technology has its drawbacks. VPNs have been criticized for being vulnerable, underperforming, and insecure, leading many organizations to explore other options for secure remote access. This article aims to explore alternative solutions that address these issues effectively.
How does VPN work
A Virtual Private Network (VPN) enables users to send and receive data over the internet through private networks. When you access the internet or other online resources, your data travels through an encrypted virtual tunnel created by the VPN. This tunnel leads to a remote server operated by the VPN provider, located in a different geographical location. As a result, your actual IP address is masked, and it seems as if you are browsing the internet from the location of the VPN server.
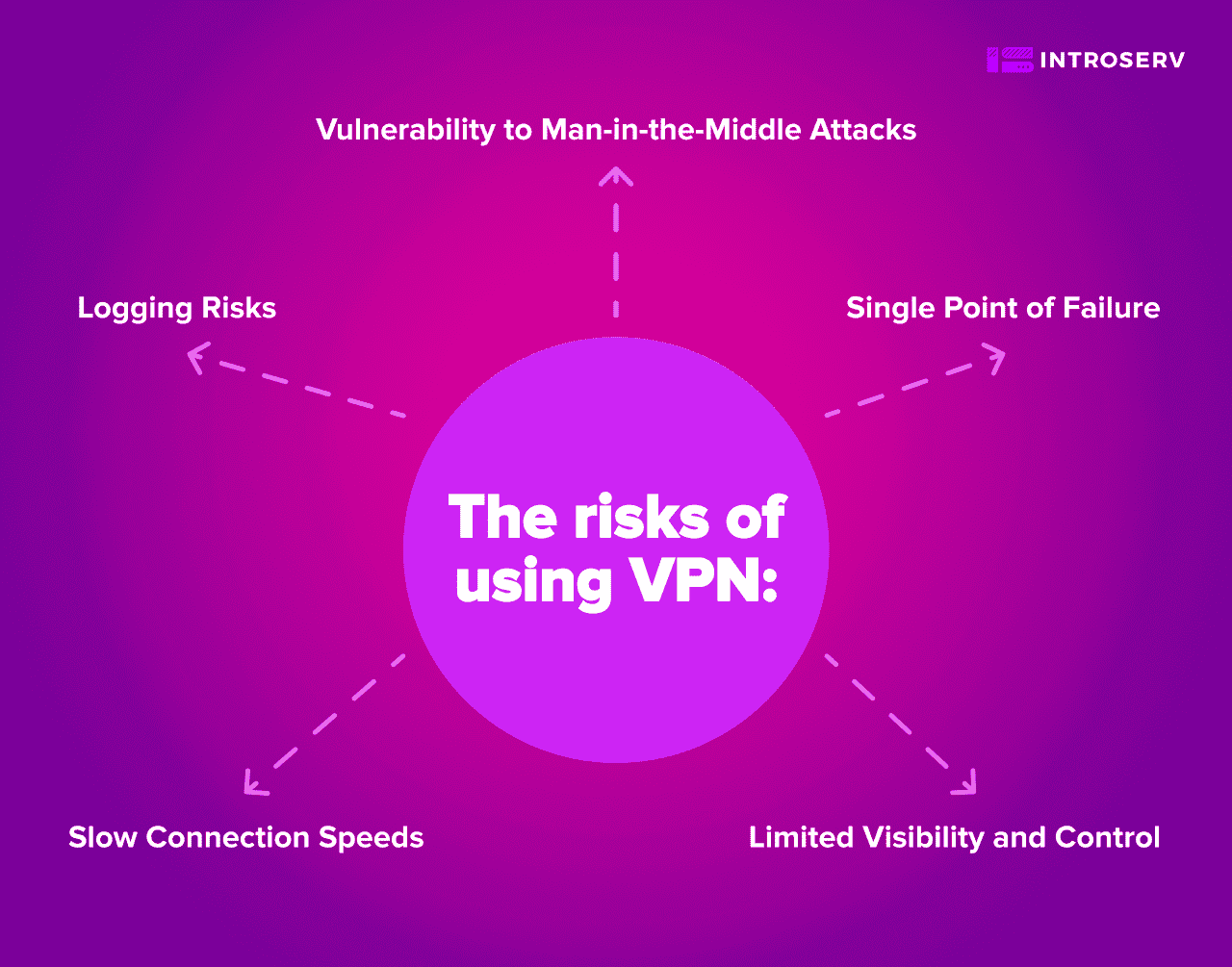
What are the risks of using VPN?
While VPNs serve as a popular choice for remote access, they have certain risks and limitations:
- Vulnerability to Man-in-the-Middle Attacks: Hackers can intercept and manipulate data transmitted through a VPN, compromising its security.
- Limited Visibility and Control: Lack of real-time visibility into user activities and network traffic hampers threat detection.
- Slow Connection Speeds: The encryption process can slow down data transmission and application performance.
- Logging Risks: Some VPNs may record your online activities, compromising your privacy and anonymity.
- Single Point of Failure: The central VPN server becomes a single point of failure, so any disruption affects all users.
The Best VPN Alternatives for Secure Remote Access:
1) Zero Trust Network Access (ZTNA):
Zero Trust Network Access (ZTNA) is a modern security approach that guarantees only authorized users and devices can access specific resources. Unlike traditional VPNs that grant broad network access, ZTNA follows the principle of "never trust, always verify". It means no user or device is automatically trusted, despite their location or previous access. This approach reduces the chances of unauthorized entry and makes it harder to breach the system.
ZTNA continuously monitors user behavior in real-time and adjusts access privileges based on activities. It helps promptly detect and address any suspicious actions, further protecting the network and its resources.
Benefits:
- Reduces the attack surface by limiting the exposure of the network and the resources to only authorized users and devices
- Improves performance by optimizing the network traffic and reducing latency.
- Simplifies management by eliminating the need for complex VPN configurations and updates.
Use Cases:
- Providing secure access to critical business applications for remote employees.
- Safeguarding sensitive data and intellectual property from unauthorized access.
- Enabling secure access for contractors and business partners while maintaining data security.
Verdict: ZTNA effectively replaces VPN by adopting a security-first approach with least-privilege access and continuous monitoring. Its focus on proactive security measures makes it a superior choice for businesses and individuals working remotely.
2) Software-Defined Perimeter (SDP):
Software-Defined Perimeter (SDP) is a security model that follows the "zero-trust" principle to ensure network access is granted only to verified users and devices. Instead of exposing the entire network surface area like a VPN, SDP takes a more targeted approach by creating micro-perimeters around individual applications. This means that users can access only the specific applications they are authorized to use, greatly reducing the risk of unauthorized access. With a "deny-all" policy, SDP starts by blocking all access and then selectively granting permissions based on user identity and other factors.
Benefits:
- Minimizes exposure by hiding the network and the resources from unauthorized or unauthenticated users and devices.
- Increases control by allowing organizations to define and enforce granular access policies for each resource.
- Reduces complexity by eliminating the need for VPN clients, servers, or tunnels.
Use Cases:
- Providing secure remote access for employees, contractors, and third-party vendors.
- Protecting critical applications and data from potential breaches.
- Facilitating secure access to cloud-based resources and SaaS.
Verdict: SDP is an excellent VPN alternative, offering enhanced security through granular access control and reduced exposure of the network surface area. Its focus on precise access permissions makes it ideal for businesses and remote workers.
3) Remote Desktop Protocol (RDP):
With Remote Desktop Protocol (RDP), users can securely access their work computer or virtual machine from any remote location. While VPNs provide broad network access and SDP restricts users to authorized applications, RDP creates a direct, focused connection to the specific remote machine needed. This connection limits the risk of unauthorized entry, as users interact only with the designated machine and not the entire network.
RDP allows you to view and interact with the server's desktop as if you were sitting in front of it. In addition, it offers easy management and monitoring of user sessions for a smooth and secure remote desktop access experience.
Benefits:
- Saves bandwidth by transmitting only the graphical changes on the screen, rather than the entire data stream.
- Enables multitasking by allowing the user to run multiple applications on the remote computer without affecting the local computer.
- Supports multiple platforms by allowing the user to connect to a remote computer running Windows, Linux, or Mac OS from any device.
Use Cases:
- Enabling remote work scenarios where employees need access to their work desktops.
- Providing technical support and troubleshooting for remote users.
- Allowing secure access to specific resources on individual machines without granting full network access.
Verdict: RDP is a great solution for secure remote desktop access and management. While it may not fully replace VPNs for all network-wide access needs, it offers improved safety and efficiency for remote workers.
4) Secure Access Service Edge (SASE):
Secure Access Service Edge (SASE) represents a comprehensive approach that combines networking and security functions in the cloud. Rather than relying on on-premises hardware and complex configurations like traditional VPNs, SASE leverages cloud-based services to provide direct and secure access to applications and resources.
SASE simplifies network management by centralizing security policies and controls, reducing the need for physical hardware and manual configurations. This method ensures secure connections and data protection for remote users, regardless of their location.
Benefits:
- Enhances scalability by allowing organizations to add or remove users or devices without affecting the network performance or security.
- Improves visibility by providing centralized monitoring and reporting of the network activity and security events
- Boosts efficiency by reducing the operational costs and complexity of managing multiple network and security solutions.
Use Cases:
- Providing secure access to cloud-based applications and resources for remote employees
- Enhancing security for remote branch offices and mobile workers.
- Facilitating secure access to SaaS and collaboration tools.
Verdict: SASE is a robust solution that can effectively replace traditional VPNs for cloud-based resources, offering improved network performance and security for remote workers and businesses.
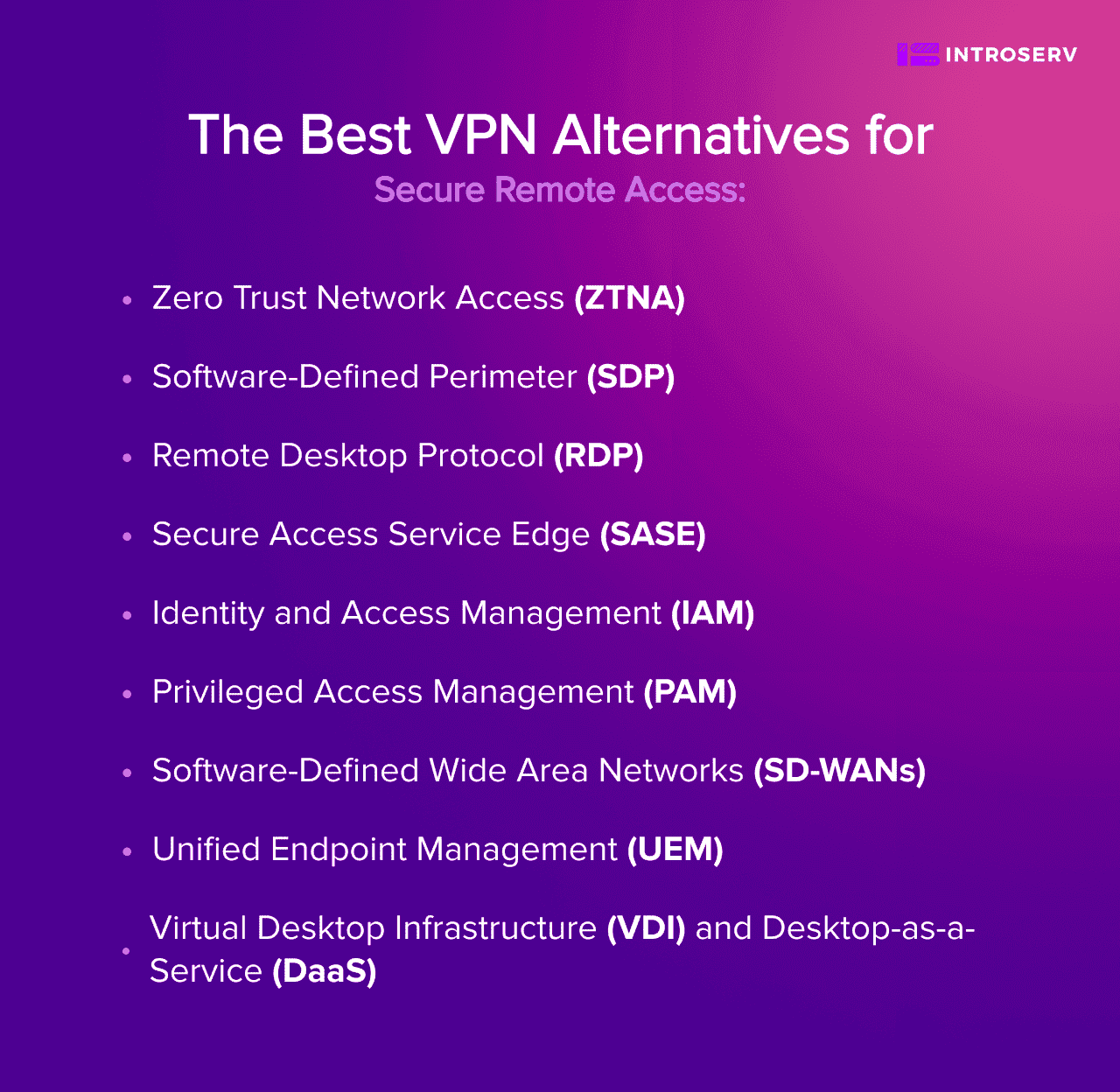
5) Identity and Access Management (IAM):
Identity and Access Management (IAM) is a comprehensive framework that focuses on centralizing user identity management and authentication. The main goal of IAM is to secure that only authorized users can access specific resources based on their roles and privileges. To achieve this, IAM employs robust authentication mechanisms, such as multi-factor authentication. This measure improves security by verifying user identities before granting access.
IAM makes access control easier by managing user identities in one place. This simplifies granting and revoking access permissions, managing user accounts, and their privileges.
Benefits:
- Strengthens security by preventing unauthorized or compromised users or devices from accessing sensitive or critical resources.
- Enhances compliance by ensuring that the access rights of users and devices are aligned with the organization’s policies and regulations.
- Boosts productivity by enabling users and devices to access the resources they need quickly and easily.
Use Cases:
- Securing access to critical applications, databases, and cloud services.
- Efficiently managing user access for remote employees and third-party vendors.
- Assuring compliance with regulatory requirements by maintaining strict access controls.
Verdict: IAM complements VPN alternatives by providing centralized identity management and strong authentication. While it addresses access control, it does not directly replace the need for secure server connectivity provided by VPNs.
6) Privileged Access Management (PAM):
Privileged Access Management (PAM) is dedicated to securing accounts, which have elevated access to critical systems and data. PAM solutions control and monitor privileged access to prevent unauthorized users from gaining entry. The strategy uses fine-grained access controls and just-in-time access to limit exposure to sensitive data.
Real-time monitoring and session recording provide visibility into privileged user activities, helping IT administrators detect and address suspicious activities promptly. By implementing PAM, organizations protect important servers, databases, and network devices from unauthorized access and data breaches.
Benefits:
- Reduces the risk of data breaches and human errors by limiting the exposure and misuse of the privileged accounts and credentials.
- Improves compliance by ensuring that the privileged access rights are aligned with the principle of least privilege and the organization’s policies and regulations.
- Increases productivity by enabling the privileged users or applications to access the resources they need securely and efficiently.
Use Cases:
- Securing administrative access to servers, databases, and network devices.
- Guaranteeing conformity with industry regulations and data protection standards.
- Safeguarding against data breaches and unauthorized access to critical assets.
Verdict: PAM is a valuable addition to VPN alternatives, as it strengthens security for privileged accounts and critical systems. However, it does not offer the direct network access required to connect to servers without a VPN.
7) Software-Defined Wide Area Networks (SD-WANs):
Software-Defined Wide Area Networks (SD-WANs) optimize network performance by intelligently routing traffic over various network connections, such as MPLS, broadband, and LTE. Unlike traditional VPNs, which route all traffic through a central gateway, SD-WANs dynamically direct traffic based on application priority, network conditions, and user requirements.
This dynamic traffic routing provides optimal performance for applications, even in remote locations. SD-WANs also economically use multiple network connections, letting groups tap into public and private networks without security gaps.
Benefits:
- Improve reliability by providing redundancy and failover mechanisms for each WAN link.
- Enhance performance by prioritizing and accelerating critical applications and traffic.
- Reduce costs by leveraging cheaper and more available WAN links such as broadband internet.
Use Cases:
- Optimizing network performance for remote and branch offices.
- Facilitating secure and high-quality access to cloud-based applications.
- Maintaining seamless connectivity for remote workers.
Verdict: SD-WANs enhance network performance and provide a cost-effective alternative to traditional VPNs. However, they do not provide the same level of secure server connectivity as VPN alternatives.
8) Unified Endpoint Management (UEM):
Unified Endpoint Management (UEM) is like a control center for businesses. It helps them manage and keep safe all sorts of devices, like laptops, phones, and tablets. Think of it as a super organized system that works with mobile device management (MDM) and mobile application management (MAM) solutions to make sure everything is secure and working well.
Admins can enforce security rules and settings across all devices from a single control center, ensuring consistent security measures for both remote and in-office devices. UEM also offers features like remote wiping and encryption to safeguard sensitive data on devices, even if they are lost or stolen.
Benefits:
- Supports BYOD (bring your own device) by allowing users to use their personal devices for work purposes without compromising security or privacy.
- Enhances user experience by providing consistent and seamless access to the resources across different devices and platforms.
- Simplifies administration by reducing the complexity and cost of managing multiple device types and solutions.
Use Cases:
- Managing and securing remote devices used by remote workers.
- Enforcing security policies for “bring your own device” (BYOD) environments.
- Protecting sensitive data and applications accessed from various endpoints
Verdict: UEM assures endpoint security but does not directly address network access to servers or provide a complete VPN replacement.
9) Virtual Desktop Infrastructure (VDI) and Desktop-as-a-Service (DaaS):
Virtual Desktop Infrastructure (VDI) and Desktop-as-a-Service (DaaS) provide secure remote access to virtualized desktops hosted on servers. Each user receives a unique and isolated virtual desktop space. This keeps their data and apps safe on the server and lowers the chance of data loss or unauthorized access.
VDI means setting up and handling virtual desktops on your own organization's systems, whereas DaaS is like a cloud option where another company takes care of hosting and managing the virtual desktops for you.
VDI and DaaS make it easy to adjust the number of virtual desktops for remote work. They can be added or removed as needed. Centralized management simplifies software updates and security patches. As a result, security measures are consistent across all virtual desktops.
Benefits:
- Increases security by storing and processing all data on the server rather than on the local device.
- Improves performance by delivering high-quality graphics and audio to the users regardless of their network bandwidth or device capability.
- Enhances scalability by allowing organizations to add or remove virtual desktops as needed without affecting the server capacity or performance.
Use Cases:
- Providing secure access to corporate desktops for remote and mobile workers.
- Enhancing data security by keeping sensitive information within the server environment.
- Facilitating quick and efficient provisioning of desktops for temporary workers and contractors.
Verdict:
VDI/DaaS is a valuable tool for secure desktop access and data isolation in remote work scenarios. But it does not replace the need for secure network access and server connectivity provided by VPNs.
Thus, the shortcomings of VPNs have prompted a surge of alternatives, each a unique key or complement to unlock a safer and faster connection. These solutions keep your data safe, your connection speedy, and your work flexible no matter where you are.






















































